AI-Powered Verification
Use AI across multiple methods to identify synthetic identities and automate risk decisions with policy controls.
- Compatible with Anthropic, Bedrock, Gemini, and OpenAI
- Automates cross-method evidence analysis
Launch adaptive verification in three simple steps using API events, hosted links, email, SMS, and custom risk logic.
Initiate a workflow from your app, CRM, or fraud engine and route users by risk profile.
Users complete the required checks while higher-risk sessions escalate to stronger proof.
Receive evidence, confidence signals, and decision outcomes to automate approval and review.
From passive bot detection to biometric liveness and document proofing, combine 20+ methods into workflows that stay simple for good users and strict for high-risk actors.
Use AI across multiple methods to identify synthetic identities and automate risk decisions with policy controls.
Make selfie liveness and live actions first-class controls for AI-generated identity attacks and spoofing attempts.
A military-grade arsenal for every threat vector.
Orchestrate decisioning using top-tier models (Anthropic, Bedrock, Gemini, OpenAI). Automatically cross-reference biometric and document evidence to detect synthetic identities and deepfakes with zero manual effort.
Require a live video selfie to confirm the user is present and human. Detects presentation attacks (masks, screens) and matches the face biometrically to the provided ID.
Authenticate users via active voice challenges. Analyze audio for synthetic voice generation (AI spoofing) and use voice biometrics for recurring authentication.
Conduct real-time video interviews with agents for high-stakes verification. Capture audit-ready evidence and deter fraudsters who refuse face-to-face interaction.
Leverage device-native biometrics (TouchID, FaceID) for passwordless authentication. Ensures the same physical user is present for every session, blocking remote bots.
Route complex cases to human analysts. Provide a unified dashboard with all data signals for expert review, reducing false positives and edge-case friction.
Authenticate government-issued IDs from 200+ countries and territories. Extract PII (OCR) and validate security features to ensure the document is genuine and unaltered.
Validate residency with automated utility bill and bank statement parsing. Cross-reference name and address data against the provided ID to ensure consistency.
Send a physical OTP letter to the user’s claimed address. A definitive, high-assurance method for proving residency in high-value or regulatory use cases.
Capture legally binding digital signatures on contracts and waivers. Compare the signature against the ID document for an additional layer of identity proofing.
Cryptographically validate ePassports and eIDs by reading the NFC chip. The highest level of document assurance, making physical tampering impossible to hide.
Verify possession via OTP while analyzing carrier metadata (line type, tenure, name match). Automatically block risky VOIP numbers (Google Voice, Skype) to filter out burner phones.
Assess email tenure, domain reputation, and deliverability in real-time. Flag disposable domains and newly created inboxes to catch fraudsters before they onboard.
Confirm account ownership via secure OAuth login. Access verified name, email, and address data directly from PayPal to validate user identity without friction.
Connect directly to user bank accounts via open banking APIs. Verify account holder name, balance, and transaction history to mitigate ACH fraud and NSF risks.
Validate card possession via 3D Secure 2.0 or micro-deposits. Confirm liability shift eligibility and match billing details to prevent stolen card usage.
Verify identity through established social profiles (Google, LinkedIn, X). Analyze account age and activity patterns to distinguish real humans from bot-generated profiles.
Enforce strong 2FA possession via time-based one-time passwords (TOTP). Ideal for recurring logins and stepping up security for high-risk transactions.
Verify wallet ownership via cryptographic signing. Screen addresses against sanctions lists and risk databases (AML) to ensure compliant Web3 transactions.
Pinpoint precise user location using GPS, Wi-Fi, and cellular triangulation. Detect and block location spoofing tools, VPNs, and proxies to enforce regional compliance.
Stop bots silently with Google’s advanced behavioral analysis. Assess interaction patterns to block automated scripts without interrupting the user experience.
Challenge users with custom logic-based questionnaires. Filter out unqualified leads or collect specific compliance data during the onboarding flow.
Validate Name, Address, and DOB against official government and credit bureau databases (eIDV). Instantly flag synthetic identities and mismatched records.
Map checks to real business context, such as transaction value, account age, country, and behavioral risk. Keep trusted users moving while automatically stepping up high-risk sessions.
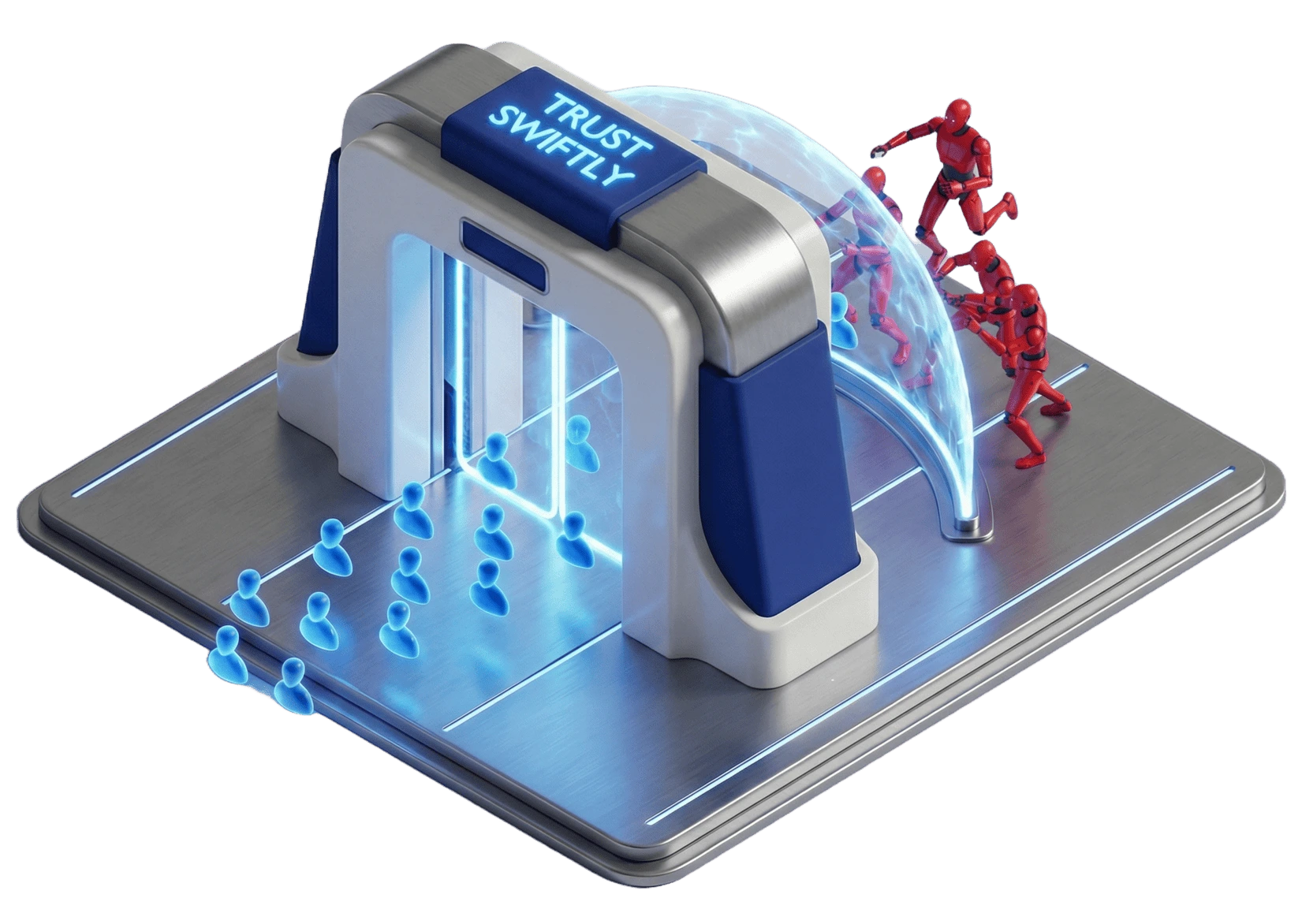
The key to effective fraud prevention isn't blocking everyone; it's intelligently identifying the right users to verify. Our platform applies dynamic friction—a targeted approach that ensures legitimate users enjoy a seamless experience while high-risk actors are met with appropriate security checks.
This precision allows you to put trusted users on the fast track and escalate only suspicious activity for verification. The result is a secure and welcoming environment that effectively combats synthetic identities, friendly fraud, and chargebacks, all while protecting your customer relationships and revenue.