The widespread shift to remote work within the U.S. federal government and its contractor supply chain has created a significant vulnerability in national security. This issue is not due to failures in network defense or endpoint detection, but rather a breakdown in remote identity verification. Nation-state actors, particularly the Democratic People's Republic of Korea (DPRK), have exploited this gap by conducting sophisticated, long-term fraudulent IT worker schemes. These operations have bypassed outdated identity controls, allowing foreign operatives to access the digital infrastructure of Fortune 500 companies, federal agencies, and defense contractors.
Initially, these schemes aimed to evade U.S. and U.N. sanctions and generate illicit revenue for North Korea's weapons programs.1 However, they have evolved into serious espionage and data extortion threats. The infiltration of a California-based defense contractor, which led to the theft of ITAR-controlled military AI data, clearly demonstrates that current remote identity proofing standards—specifically Identity Assurance Level 2 (IAL2)—are inadequate against state-sponsored actors using AI deepfakes, synthetic media, and domestic proxy networks.4
Federal system integrators, prime contractors, and technology providers subject to Executive Order 14028 and OMB Memorandum M-22-09 must recognize that standard multi-factor authentication (MFA) and unsupervised remote onboarding do not provide true security. Issuing a phishing-resistant cryptographic token (AAL3) is ineffective if the user's identity was compromised or falsified during onboarding.
This exhaustive research report provides a nuanced, deeply technical analysis of the DPRK remote IT worker threat methodology, the compounding vulnerabilities within existing federal identity systems as documented by the Government Accountability Office (GAO) and various Offices of the Inspector General (OIG), and the rapidly evolving regulatory landscape under the National Institute of Standards and Technology (NIST) Special Publication 800-63-4. Ultimately, this report establishes the imperative for organizations to immediately abandon legacy IAL2 workflows in favor of NIST IAL3 Supervised Remote Identity Proofing (SRIP) solutions, utilizing hardware-anchored cryptographic verification, to secure the federal supply chain.
The Anatomy of State-Sponsored IT Fraud: The DPRK Methodology
North Korean IT worker threats combine digital deception, physical infrastructure manipulation, and coordinated cross-border activity. These are not opportunistic attacks, but organized, state-directed operations designed to bypass unsupervised remote identity proofing (IAL2) processes widely used in the U.S. Understanding these tactics is essential to recognizing the shortcomings of current security measures.
These operations start with the creation and use of fraudulent digital identities. DPRK operatives use stolen, borrowed, or synthetic identities of U.S. citizens to secure employment in regulated sectors.1 Facilitators in the U.S. and abroad act as identity brokers, creating convincing online profiles and using web services, AI tools, and background check programs to build credible digital footprints.1 They also set up U.S.-based front companies to present North Korean workers as legitimate contract staff through domestic staffing agencies.1
The critical vulnerability exploited during the hiring phase is the remote interview and onboarding process. In many instances, the threat actors execute a sophisticated "bait-and-switch" or proxy interviewing technique. A U.S.-based facilitator, or a different individual who perfectly matches the stolen identity's demographic profile and possesses fluent English skills, attends the virtual interviews to pass the initial human resources screening and technical engineering assessments.1 Once the employment contract is secured, the background check is passed (because the identity itself is technically real, albeit stolen), and the onboarding process is complete, the actual daily IT work, access credentials, and corporate network access are immediately handed over to the North Korean operative located overseas.
When proxy interviewers are not used, North Korean operatives rely on advanced generative AI to manipulate their digital presence. The FBI has issued urgent warnings about deepfakes—AI-generated media used to impersonate job applicants during online interviews and bypass remote identity verification.6 These technologies alter voice and facial appearance in real time, and while some anomalies may occur, deepfakes are increasingly sophisticated and often deceive HR personnel.6
The rise of generative AI tools that create fake resumes, realistic images, and voice clones has caused a surge in fraudulent applicants for remote technical roles.7 Standard IAL2 verification, which relies on automated comparisons of selfies and ID scans, is increasingly unable to detect sophisticated injection or presentation attacks enabled by these technologies.
A key feature of the DPRK IT worker scheme is the use of domestic physical proxy networks, known as "laptop farms," to evade geolocation and endpoint security controls.4
Federal agencies and their cleared defense contractors routinely ship expensive, corporate-owned, heavily monitored laptops to the physical U.S. addresses provided by their new "remote employees" during the onboarding phase. In reality, these addresses belong to the witting U.S.-based facilitators.1 Upon receiving the corporate devices, the facilitators do not log into them directly. Instead, they connect the corporate laptops to their own residential U.S. broadband networks and attach Keyboard-Video-Mouse (KVM) over IP devices, or in some cases, install unauthorized remote desktop software.1
This physical infrastructure creates an impenetrable blind spot for corporate IT and security teams. When the North Korean IT worker overseas connects to the KVM device via the internet, they take complete, low-level control of the corporate laptop. The KVM hardware takes the physical video output of the laptop, digitizes it, and sends it to the overseas attacker, while taking the attacker's remote keystrokes and injecting them directly into the laptop's physical USB ports. To the employer's endpoint detection and response (EDR) software, network monitoring tools, and identity providers (IdP), the employee appears to be working entirely within the United States, utilizing the authorized, fully patched corporate device, typing on a local keyboard, and adhering to all geographic conditional access policies.1 This physical proxy mechanism completely and flawlessly neutralizes the defensive value of traditional IP filtering, geo-fencing, standard device trust signals, and software-based location tracking.
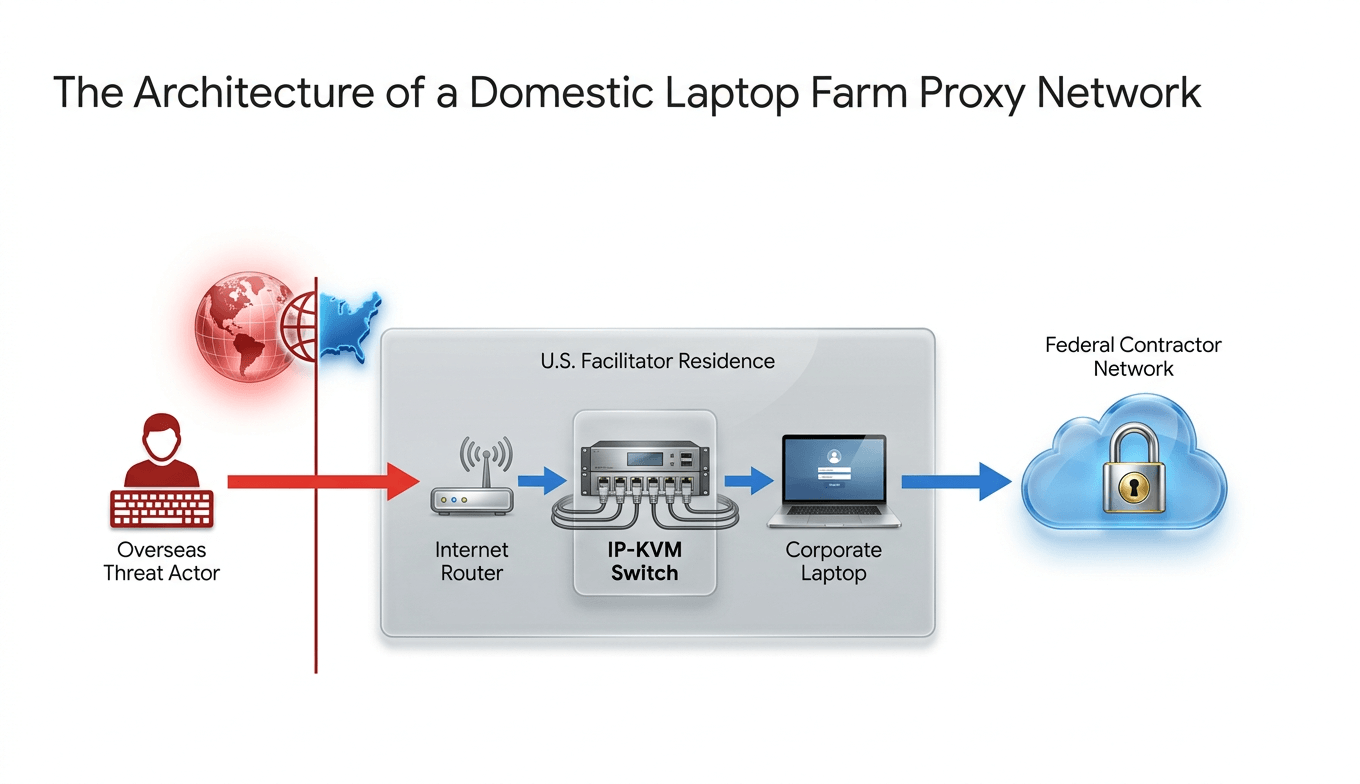
North Korean IT workers bypass corporate geographic restrictions by routing their connections through U.S.-based facilitators. The facilitator receives the corporate laptop, connects it to an IP-KVM switch, and grants the overseas actor remote control. To the corporate network, all telemetry suggests the device is operating securely within U.S. borders.
Glaring Compromises in the Federal Supply Chain and Government Networks
Assuming these fraudulent workers only seek low-level coding jobs is a serious underestimation of the threat. Recent actions by the DOJ, FBI, and DCIS show that these actors are infiltrating sensitive environments, stealing data, inserting malicious code, and extorting employers.
A significant escalation occurred between January 19 and April 2, 2024, when an overseas co-conspirator remotely accessed the secure systems of a California-based defense contractor specializing in military AI technologies.4 This case highlights the urgent need for IAL3 in the defense sector.
The North Korean IT worker bypassed standard hiring and identity verification using a U.S. identity broker, then used authorized access to steal sensitive technical data, proprietary algorithms, and source code, including ITAR-controlled specifications.4
This incident is not isolated; it reveals a systemic failure in national supply chain security. ITAR regulations require strict access controls to prevent foreign nationals from accessing defense data. The ability of a North Korean operative to obtain an IT position, receive a corporate device, and exfiltrate ITAR-controlled technology shows that current remote onboarding processes are inadequate. For organizations serving the DoD or intelligence community, relying on IAL2 for remote workers now poses unacceptable security risks.
The sheer scale and economic impact of the DPRK infiltration across the broader economy is staggering, further validating the urgent need for systemic reform. In a massive series of coordinated law enforcement actions spanning 2024 and 2025, the Justice Department unsealed indictments against dozens of individuals, executing search warrants at 29 known or suspected "laptop farms" across 16 different states.4 Law enforcement seized approximately 200 corporate computers that had been repurposed as KVM proxies, 29 financial accounts used to launder funds, and 21 fraudulent websites used to prop up the synthetic identities.4
U.S. facilitators, including Zhenxing "Danny" Wang and Kejia "Tony" Wang, were arrested for running multi-year fraud schemes.4 They used shell companies to receive equipment and host proxy networks, enabling North Korean IT workers to earn millions from U.S. companies.4 Over 300 companies were affected,2 with one case involving 136 victim firms and $2.2 million in illicit revenue, as well as the compromise of 18 U.S. citizens' identities.5
The revenue generation capabilities of these networks are industrial in scale. Conspirators working for DPRK-controlled front companies located in China (such as Yanbian Silverstar) and Russia (Volasys Silverstar) were explicitly ordered by their military superiors to earn at least $10,000 per month each through remote tech jobs.10 One specific six-year conspiracy alone generated at least $88 million in illicit salaries.10 This capital is routinely laundered through complex networks involving U.S. and Chinese financial systems, and increasingly via obfuscated cryptocurrency platforms, directly funding the North Korean government's strategic priorities.9
The FBI has noted a shift in tactics: DPRK IT workers now use their access to steal credentials, copy proprietary code to personal cloud accounts, and extort employers by threatening to leak or sell the data.2 Some introduce malicious code and backdoors for future exploitation by North Korean hacking units, such as APT38, which has conducted major virtual currency heists.103
Critically, the threat is not receding—it is accelerating. On February 19, 2026, a Ukrainian national was sentenced in federal court in the District of Columbia for operating a laptop farm scheme that directly generated income for North Korean IT workers.34 This sentencing, occurring just days before this report's publication, underscores the persistent and growing nature of these operations. Despite years of coordinated federal enforcement, new facilitators continue to emerge, new laptop farms continue to be established, and the underlying vulnerability in remote identity verification that enables the entire scheme remains fundamentally unaddressed by legacy IAL2 controls.
| Incident / Threat Actor Profile | Target Sector & Scope | Primary Impact / Stolen Assets | Method of Entry / Exploitation |
|---|---|---|---|
| DPRK Operative (Jan-Apr 2024) | CA-Based Defense Contractor | ITAR-controlled military AI data, Proprietary Source Code4 | Fraudulent remote hire via U.S. identity broker and KVM proxy4 |
| APT38 (DPRK Military Hacking Group) | Global Virtual Currency Platforms | Multi-million dollar virtual currency heists (Over $15M seized by DOJ)5 | Exploitation of trusted network access, lateral movement5 |
| Zhenxing Wang / Kejia Wang Network | Fortune 500 / Over 136 U.S. Companies | $5M+ in illicit salaries, widespread corporate network infiltration4 | Operated massive domestic "Laptop Farms" across 16 states4 |
| Yanbian Silverstar Conspirators | General Corporate / U.S. Non-Profits | $88M generated, Source code theft, Aggressive Extortion campaigns10 | Synthetic identities, false documentation, organized labor deployment10 |
Systemic Deficiencies in Federal Identity Architecture
The crisis of remote identity verification extends far beyond the vulnerabilities of private sector contractors; it strikes deep into the heart of the federal government itself. Independent audits and rigorous investigations by federal oversight bodies over recent years have repeatedly highlighted the extreme fragility of legacy federal identity systems when confronted with modern, scalable fraud techniques.
A highly critical June 2025 report published by the Government Accountability Office (GAO-25-107000) exposed significant historical and systemic deficiencies in federal identity verification capabilities, specifically targeting the core infrastructure meant to protect government data.12 Login.gov, the General Services Administration's (GSA) centralized authentication tool used by millions of citizens and federal employees to access secure government services, was found to be lagging severely behind commercial standards in combating identity fraud.14
The GAO meticulously noted that between fiscal years 2020 and 2023, Login.gov did not provide identity proofing services that fully aligned with the National Institute of Standards and Technology's (NIST) IAL2 standards, let alone the rigorous requirements of IAL3.14 Specifically, the system critically lacked any robust biometric verification capabilities during this multi-year period.14 While the GSA has recently taken steps to align Login.gov with NIST guidance—including rolling out manual, in-person identity proofing functionalities at local post offices and piloting updated remote proofing tools—the historical lack of cryptographic biometrics allowed vast swaths of synthetic and stolen identities to permeate federal systems.15 The report underscores a fundamental truth: traditional knowledge-based authentication (KBA), simple credit checks, and basic document uploads—the hallmarks of weak, legacy remote proofing—are entirely insufficient to stop dedicated, resourced identity thieves.
The Department of Homeland Security's (DHS) E-Verify system, strictly mandated for federal employment eligibility verification, suffers from parallel and highly exploitable vulnerabilities. A DHS Office of Inspector General (OIG) report (OIG-21-56) identified profound deficiencies in E-Verify's processes for confirming a subject's identity during employment verification.17
The core vulnerability within E-Verify lies in its antiquated photo matching process. E-Verify does not utilize automated, cryptographic, or biometric liveness detection to mathematically match a prospective employee against their official documentation. Instead, it relies almost entirely on the subjective, highly fallible manual review of photos by the employer's human resources representative.17 In a remote onboarding scenario, an HR representative sitting in Virginia is asked to visually compare a potentially deepfaked video feed originating from a laptop farm in Arizona against a scanned, potentially photoshopped identity document. This reliance on human visual inspection to detect advanced synthetic media, voice cloning, and AI-generated forgeries is a critical systemic failure. It renders E-Verify practically defenseless against the sophisticated deception tactics employed by DPRK IT workers.1 Furthermore, aggressive enforcement of child labor laws and stringent E-Verify compliance mandates mean that employers face strict legal liability and immense fines for violations, even if they were actively and maliciously deceived by state-sponsored generative AI.7
These acute identity vulnerabilities are compounded by broader, deeply concerning cybersecurity lapses across major federal agencies, highlighting a pervasive inability to secure remote operational environments. The Treasury Inspector General for Tax Administration (TIGTA) reported in an exhaustive 2025 audit that the Internal Revenue Service's (IRS) Cybersecurity Program was officially considered "not effective."18 Specifically, the IRS failed in its core capabilities to Identify, Protect, and Detect cybersecurity threats against its massive repository of taxpayer data.18 Similarly, the Consumer Financial Protection Bureau (CFPB) Office of Inspector General noted a definitive decrease in the maturity of the CFPB's information security program, citing the continued use of outdated software, failure to maintain authorizations to operate, and inadequate risk acceptance analysis across the enterprise.19 Additionally, the Department of Health and Human Services (HHS) OIG found that numerous federal contractors were failing to include required cybersecurity language in their contracts and failing to report critical breaches within mandated timeframes.20
The implication of these reports is stark. If heavily resourced federal agencies themselves struggle to maintain basic cyber hygiene and fail to detect intrusions, the expectation that their sprawling, highly decentralized network of remote contractors can independently defend against nation-state identity spoofing without centralized, mandated, high-assurance identity solutions is strategically unsound and practically impossible.
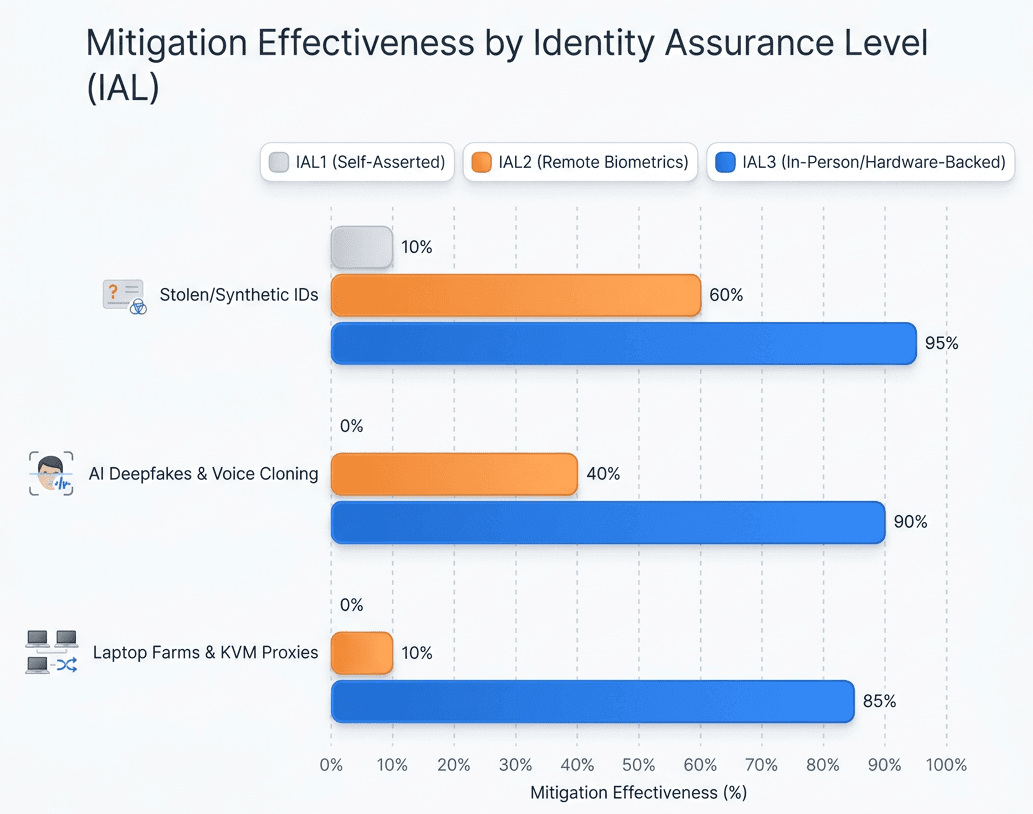
While IAL2 (Unsupervised Remote Proofing) offers moderate protection against basic identity theft, it is highly vulnerable to AI Deepfakes and completely ineffective against physical proxy evasion (Laptop Farms). Only IAL3 (Supervised Remote Identity Proofing with Hardware Anchors) provides high confidence mitigation across all advanced state-sponsored attack vectors. Data sources: NIST SP 800-63-4, NIST Guidelines, NIST Implementation Resources
The Regulatory Imperative: EO 14028, OMB M-22-09, and NIST 800-63-4
The federal government has fully recognized the escalating severity of the threat landscape and has responded by issuing a series of sweeping, transformative mandates intended to enforce a strict Zero Trust architecture across all civilian agencies, the Department of Defense, and the broader contractor ecosystem. However, successfully navigating these regulations and achieving true security requires a highly precise understanding of the critical interplay between ongoing authentication (AAL) and initial identity proofing (IAL).
Executive Order 14028, "Improving the Nation's Cybersecurity," fundamentally reordered federal IT priorities, officially mandating the rapid adoption of multi-factor authentication and encryption for data at-rest and in-transit.21 This executive directive was rapidly operationalized by OMB Memorandum M-22-09, which set a stringent new baseline for access controls. M-22-09 explicitly requires all federal agencies to implement phishing-resistant MFA (such as WebAuthn protocols or PIV smart cards) and forcefully mandates the discontinuation of vulnerable authentication methods, including SMS texts, voice calls, or simple push notifications.23
While M-22-09 correctly and aggressively addresses the threat of credential harvesting, man-in-the-middle phishing, and MFA fatigue attacks (effectively forcing organizations to achieve Authenticator Assurance Level 3, or AAL3), it creates a perilous, systemic false sense of security if the underlying identity of the user is compromised at the point of origin. A phishing-resistant hardware token, such as a YubiKey or a PIV badge, is entirely useless as a security measure if it is issued and mailed to a North Korean operative who successfully spoofed an IAL2 remote onboarding process using a U.S. proxy address. The token will flawlessly, cryptographically authenticate the attacker every single time they log in. Therefore, to truly comply with the spirit, intent, and security mandate of EO 14028, organizations must secure the initial identity binding process with a level of rigor that perfectly matches the subsequent authentication process.
The National Institute of Standards and Technology clearly recognizes this critical, exploitable gap. The ongoing transition from NIST Special Publication 800-63-3 to the impending, highly rigorous 800-63-4 represents a massive paradigm shift in how digital identity risk is calculated and managed across the federal enterprise.9
Under legacy IAL2 standards, remote identity proofing generally required the applicant to merely upload a photo of a government ID alongside a self-captured photograph (a selfie) using their own personal mobile device.26 This "unsupervised" or "conventional" remote proofing relies entirely on automated, algorithmic systems to compare the images, perform basic optical character recognition (OCR), and attempt to detect superficial tampering.27 As definitively demonstrated by the DPRK's continuous success in breaching defense contractors, this automated, unsupervised process is highly vulnerable to advanced AI injection attacks (where the camera feed is bypassed entirely), deepfakes, and high-quality physical presentation attacks.
NIST 800-63-4 expands fraud requirements significantly to counter these exact threats. It integrates a new Digital Identity Risk Management (DIRM) framework that emphasizes continuous evaluation metrics and adds highly specific controls mandated for addressing sophisticated injection attacks and forged synthetic media. Crucially, the updated publication clarifies the distinct, absolute superiority of Identity Assurance Level 3 (IAL3) for mitigating advanced persistent threats.
IAL3 introduces stringent, unyielding requirements that simply cannot be met by standard, off-the-shelf remote onboarding software tools:
- Physical Presence or Supervised Remote: IAL3 strictly requires identity proofing to be performed on-site and physically attended by an authorized, trained proofing agent (a Trusted Referee). Alternatively, if physical presence is impossible, the organization must utilize rigorous Supervised Remote Identity Proofing (SRIP).26
- Specialized Hardware Controls: True SRIP requires the use of specialized, tamper-resistant equipment that remains firmly under the Credential Service Provider's (CSP) control, which is securely deployed to the remote location, explicitly forbidding the use of the applicant's personal, potentially compromised device.27
- Superior Evidence and Cryptographic Biometrics: IAL3 demands the collection of superior identity evidence and strictly requires a successful, highly accurate biometric comparison against the biometric characteristic collected during the original proofing process. This is the only acceptable mechanism to conclusively detect fraudulent enrollments, duplicate synthetic identities, and re-establish binding to a credential during recovery events.29
The regulatory trajectory is absolutely clear, and the enforcement mechanisms are tightening: for high-risk access—such as federal contractors handling ITAR data, personnel accessing critical financial infrastructure, or administrators managing cloud environments—unsupervised IAL2 is no longer a legally or operationally defensible security posture. The explicit mandate is rapidly moving toward supervised, hardware-anchored IAL3.
Solving the Crisis: The Trust Swiftly IAL3 Paradigm
To directly neutralize the glaring vulnerability of remote IT worker fraud, secure the defense supply chain, and align seamlessly with the highest echelons of federal compliance (including FedRAMP High and DoD IL4/5 authorization), federal practices and their sprawling contractor networks require a fundamental, root-and-branch overhaul of their identity verification architecture. Trust Swiftly provides the definitive, battle-tested solution through its FedRAMP-aligned IAL3 Supervised Remote Identity Proofing platform.
Trust Swiftly completely transforms the ambiguous, highly exploitable, software-only process of remote hiring into an unbreakable cryptographic chain of custody. By doing so, it effectively renders the DPRK's entire operational model—including multi-state laptop farms, IP-KVM proxies, and AI deepfakes—entirely obsolete.
The foundational failure of standard IAL2 is the inherent reliance on the user's personal, potentially compromised, or actively spoofed mobile device (BYOD) to capture and transmit identity evidence. Trust Swiftly eliminates this variable entirely by shifting to a strict, hardware-anchored verification model, achieving true, unassailable IAL3 compliance.30
Organizations deploy Trust Swiftly via two primary, highly controlled methods to scale securely across globally distributed workforces:
- On-Premise Kiosks: Managed, highly secure verification stations deployed in corporate offices, secure facilities, or controlled field locations.30 These tamper-resistant kiosks ensure superior hardware security compared to personal devices and mandate a supervised process overseen by a trained human operator, fulfilling the strictest interpretation of NIST physical presence guidelines.30
- Hardware Remote Kits: For fully distributed federal remote workers where travel to a kiosk is unfeasible, Trust Swiftly ships controlled, cryptographically certified hardware directly to the prospective employee.32 Trust Swiftly manages the entire complex lifecycle—secure shipping, real-time tracking, return logistics, and hardware attestation—ensuring the organization maintains absolute device ownership and prevents sophisticated supply chain interception or tampering.30
By forcing the identity proofing event off the user's phone and onto a controlled, tamper-evident piece of hardware, Trust Swiftly establishes a trusted execution environment. This architectural shift immediately and permanently neutralizes the threat of software-based injection attacks, where adversaries utilize virtual cameras to feed pre-recorded deepfake videos directly into the verification data stream, completely bypassing traditional 2D liveness checks.
Furthermore, Trust Swiftly moves far beyond simple visual document inspection by executing a hardware-anchored 3-Way Biometric Match. This intensive process provides unalterable digital evidence that irrefutably validates the physical person operating the device.33
This process incorporates three distinct pillars of cryptographic certainty:
- Live Facial Recognition with Certified 3D Liveness Detection: Utilizing the controlled hardware's advanced sensors, the system captures true 3D depth and liveness, instantly and conclusively detecting presentation attacks such as silicone masks, high-resolution screens, and AI-generated deepfakes that routinely defeat software-only solutions.
- Cryptographic NFC Document Verification: Rather than relying on a highly fallible optical scan (OCR) of a passport or driver's license—which can be easily photoshopped or deepfaked by state actors—the Trust Swiftly Remote Kit uses Near Field Communication (NFC) hardware to cryptographically read the secure chip embedded within modern e-Passports and mobile driver's licenses. This process mathematically validates the digital signature of the issuing government authority (conforming to ICAO Document 9303 standards). Because forging the state's private key is practically impossible, document forgery is completely eliminated as a viable attack vector.
- Human Oversight (Supervised Remote): Adhering strictly to NIST IAL3 SRIP guidelines, the entire biometric and cryptographic process is actively supervised by expert operators or the organization's trained security staff. This combines the infallibility of advanced cryptographic checks with nuanced human intuition to detect behavioral anomalies that automated systems might overlook.27
Critically, the DPRK's absolute reliance on U.S.-based facilitators and IP-KVM switches to mask their physical location is utterly and elegantly defeated by Trust Swiftly's physical hardware model.
When a defense contractor utilizes standard remote onboarding, they mail a corporate laptop to a U.S. address. The witting facilitator plugs that laptop into an IP-KVM, and the North Korean operative logs in from overseas to complete the software-based onboarding.
With Trust Swiftly's IAL3 Remote Kit, the specialized verification hardware is shipped to the applicant's stated U.S. address. To complete onboarding, the applicant must physically interact with the device. They must place their physical, cryptographically verifiable e-Passport on the physical NFC reader, and they must present their physical face to the 3D biometric sensor in real-time, all under the watchful supervision of a live remote human operator.30
A North Korean intelligence operative sitting in Pyongyang or Vladivostok cannot physically interact with a secure Remote Kit sitting in a facilitator's living room in Arizona or New Jersey. Furthermore, the U.S. facilitator cannot complete the proofing process on the operative's behalf, because the facilitator's facial biometrics will not match the stolen identity documents of the persona the North Korean is attempting to assume. The strict geographical and physical separation between the required hardware interaction and the actual overseas threat actor permanently breaks the entire laptop farm operational paradigm.
Recognizing that not every single transaction or low-level employee requires the full rigor of IAL3, Trust Swiftly provides adaptive fraud and identity controls via a unified, highly configurable platform.32 Organizations can implement intelligent, risk-based workflow orchestration. Standard users or low-risk transactions can proceed with low-friction checks. However, the system automatically triggers step-up reproofing to FedRAMP-aligned IAL3 when high-risk signals are detected—such as sudden changes in payroll routing information, anomalous login times, attempts to access sensitive ITAR repositories, or alerts from the EDR system.
Finally, Trust Swiftly automatically generates comprehensive, audit-ready evidence.32 It captures verification decisions, biometric match scores, and cryptographic artifacts in a secure, unalterable format. For federal contractors facing stringent, high-stakes compliance audits by Third-Party Assessment Organizations (3PAOs) for CMMC, FedRAMP High, or DoD IL4/5 authorization, this cryptographic chain of custody removes all ambiguity, dramatically accelerating the assessment process and providing defensible proof of compliance.32
Conclusion: Securing the Future of the Remote Workforce
The persistent threat posed by sophisticated, state-sponsored actors necessitates not only an acknowledgment of technical vulnerabilities but a decisive reorientation of identity proofing protocols within the federal supply chain. As demonstrated throughout this analysis, reliance on unsupervised, software-based solutions such as IAL2 underestimates both the scale and complexity of contemporary adversarial techniques, including AI-powered deepfakes and proxy network evasion. The rigorous examination of recent federal breaches, GAO and OIG audits, and the evolving regulatory environment underscore the systemic limitations of legacy approaches. Critically, only the implementation of NIST IAL3, anchored in supervised and hardware-verified identity proofing, can provide the cryptographic assurances required to counteract these threats effectively.
Moving forward, organizations that proactively transition to supervised, hardware-backed identity solutions—such as those exemplified by Trust Swiftly—will situate themselves at the forefront of both compliance and operational resiliency. This shift is not simply a matter of meeting regulatory requirements; it represents an essential transformation for establishing a defensible root of trust and restoring confidence in the remote workforce. Ultimately, true security in the digital era demands that federal agencies and their contractors abandon incremental fixes for comprehensive, architecture-level reforms that address the full sophistication of nation-state attack vectors. By embracing this imperative, the federal supply chain can achieve both enduring security and compliance, safeguarding the nation's critical operations in an era of unprecedented technological risk.
The defense against this highly sophisticated, state-sponsored threat cannot be found in minor, iterative updates to existing software-based identity verification workflows. The threat landscape demands a structural, uncompromising paradigm shift. The adoption of NIST IAL3 standards, rigorously enforced through Trust Swiftly's hardware-anchored, supervised remote verification platform, provides the cryptographic certainty necessary to sever the proxy networks, expose synthetic deepfakes, and restore the operational integrity of the federal supply chain.
Implementing IAL3 is no longer merely an exercise in fulfilling compliance checklists; it is an urgent, non-negotiable mandate for the protection of national security. By moving from a vulnerable software-only model to an authoritative, hardware-backed root of trust, organizations can permanently neutralize the remote IT worker vulnerability and ensure their operations remain secure, compliant, and deeply resilient against modern industrial espionage.
Works Cited
- North Korean IT Worker Threats to U.S. Businesses — FBI, https://www.fbi.gov/investigate/cyber/alerts/2025/north-korean-it-worker-threats-to-u-s-businesses
- Privacy, Cyber & Data Strategy / Immigration Advisory | North Korean IT Remote Worker Fraud Scheme Data Security and Employment Law Impact | News & Insights | Alston & Bird, https://www.alston.com/en/insights/publications/2025/01/north-korea-it-fraud-scheme-data-security-law
- Sanctions Imposed on DPRK IT Workers Generating Revenue for the Kim Regime | U.S. Department of the Treasury, https://home.treasury.gov/news/press-releases/sb0190
- Office of Public Affairs | Justice Department Announces Coordinated ..., https://www.justice.gov/opa/pr/justice-department-announces-coordinated-nationwide-actions-combat-north-korean-remote
- Justice Department Announces Nationwide Actions to Combat Illicit North Korean Government Revenue Generation, https://www.justice.gov/opa/pr/justice-department-announces-nationwide-actions-combat-illicit-north-korean-government
- FBI Warns That Scammers Are Using Deepfakes to Apply for Sensitive Jobs - WilmerHale, https://www.wilmerhale.com/en/insights/blogs/wilmerhale-privacy-and-cybersecurity-law/20220701-fbi-warns-that-scammers-are-using-deepfakes-to-apply-for-sensitive-jobs
- AI, Deepfakes, and the Rise of the Fake Applicant – What Employers Need to Know, https://www.bradley.com/insights/publications/2025/06/ai-deepfakes-and-the-rise-of-the-fake-applicant-what-employers-need-to-know
- NIST SP 800-63 Digital Identity Guidelines, https://pages.nist.gov/800-63-4/
- DOJ Announces Major Enforcement Actions Targeting North Korean Remote IT Worker Schemes | Crowell & Moring LLP, https://www.crowell.com/en/insights/client-alerts/doj-announces-major-enforcement-actions-targeting-north-korean-remote-it-worker-schemes
- Fourteen North Korean Nationals Indicted for Carrying Out Multi-Year Fraudulent Information Technology Worker Scheme and Related Extortions - Justice.gov, https://www.justice.gov/archives/opa/pr/fourteen-north-korean-nationals-indicted-carrying-out-multi-year-fraudulent-information
- North Korean IT Workers Conducting Data Extortion - FBI, https://www.fbi.gov/investigate/cyber/alerts/2025/north-korean-it-workers-conducting-data-extortion
- GSA Should Demonstrate Its Implementation of Policies for Testing Data Backups on Login.gov - GAO, https://files.gao.gov/reports/GAO-25-107000/index.html
- IDENTITY VERIFICATION: GSA Should Demonstrate Its Implementation of Policies for Testing Data Backups on Login.gov - GAO, https://www.gao.gov/assets/gao-25-107000.pdf
- Identity Verification: GSA Should Demonstrate Its Implementation of Policies for Testing Data Backups on Login.gov - GAO, https://www.gao.gov/products/gao-25-107000
- GAO-24-106640, IDENTITY VERIFICATION: GSA Needs to Address NIST Guidance, Technical Issues, and Lessons Learned - GAO.gov, https://files.gao.gov/reports/GAO-25-106640/index.html
- IDENTITY VERIFICATION GSA Needs to Address NIST Guidance, Technical Issues, and Lessons Learned - GAO, https://www.gao.gov/assets/880/873916.pdf
- USCIS Needs to Improve Its Electronic Employment Eligibility Verification Process | Office of Inspector General - OIG.dhs.gov, https://www.oig.dhs.gov/reports/2021/uscis-needs-improve-its-electronic-employment-eligibility-verification-process/oig-21-56-aug21
- The IRS's Cybersecurity Program Was Not Effective for Fiscal Year 2025 - Treasury Inspector General for Tax Administration, https://www.tigta.gov/sites/default/files/reports/2025-09/2025200037fr.pdf
- 2025 Audit of the CFPB's Information Security Program - OIG: Office of Inspector General, https://oig.federalreserve.gov/reports/cfpb-information-security-program-oct2025.htm
- Deficiencies With Incorporating Required Cybersecurity Language in HHS Contracts and Timeliness of Contractor Incident Reporting | Office of Inspector General | Government Oversight | U.S. Department of Health and Human Services, https://oig.hhs.gov/reports/all/2025/deficiencies-with-incorporating-required-cybersecurity-language-in-hhs-contracts-and-timeliness-of-contractor-incident-reporting/
- Improving the Nation's Cybersecurity - Federal Register, https://www.federalregister.gov/documents/2021/05/17/2021-10460/improving-the-nations-cybersecurity
- Executive Order on Improving the Nation's Cybersecurity - CISA, https://www.cisa.gov/topics/cybersecurity-best-practices/executive-order-improving-nations-cybersecurity
- Executive Order on Improving the Nation's Cybersecurity | Yubico, https://www.yubico.com/solutions/executive-order-hub/
- M-22-09 Federal Zero Trust Strategy - The White House, https://www.whitehouse.gov/wp-content/uploads/2022/01/M-22-09.pdf
- SP 800-63-4, Digital Identity Guidelines - NIST CSRC, https://csrc.nist.gov/pubs/sp/800/63/4/ipd
- NIST.SP.800-63-3.pdf, https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-63-3.pdf
- SP 800-63A: IAL2 Remote Identity Proofing - NIST Pages, https://pages.nist.gov/800-63-3-Implementation-Resources/63A/ial2remote/
- Identity Proofing Requirements - NIST Pages, https://pages.nist.gov/800-63-4/sp800-63a/ial/
- NIST Special Publication 800-63A, https://pages.nist.gov/800-63-3/sp800-63a.html
- Trusted Supervised Remote ID Verification - Trust Swiftly, https://trustswiftly.com/trusted-supervised-remote-id-verification/
- Federal Identity, Credential, and Access Management Sub Committee - IDManagement.gov, https://www.idmanagement.gov/implement/mapping-of-sp800-53-ia-to-sp-800-63/
- Trust Swiftly | Identity Verification and FedRAMP-Aligned IAL3 Proofing, https://trustswiftly.com/
- IAL3 Verification Solution | NIST 800-63A Compliant & FedRAMP Ready | Trust Swiftly, https://trustswiftly.com/nist-ial3-verification/
- Ukrainian National Sentenced for Laptop Farm Scheme that Generated Income for North Korean IT Workers - U.S. Attorney's Office, District of Columbia, https://www.justice.gov/usao-dc/pr/ukrainian-national-sentenced-laptop-farm-scheme-generated-income-north-korean-it-workers