Risk-Based Workflow Orchestration
Trigger stronger verification only when signals indicate risk, so low-risk users move quickly while high-risk events get deeper checks.
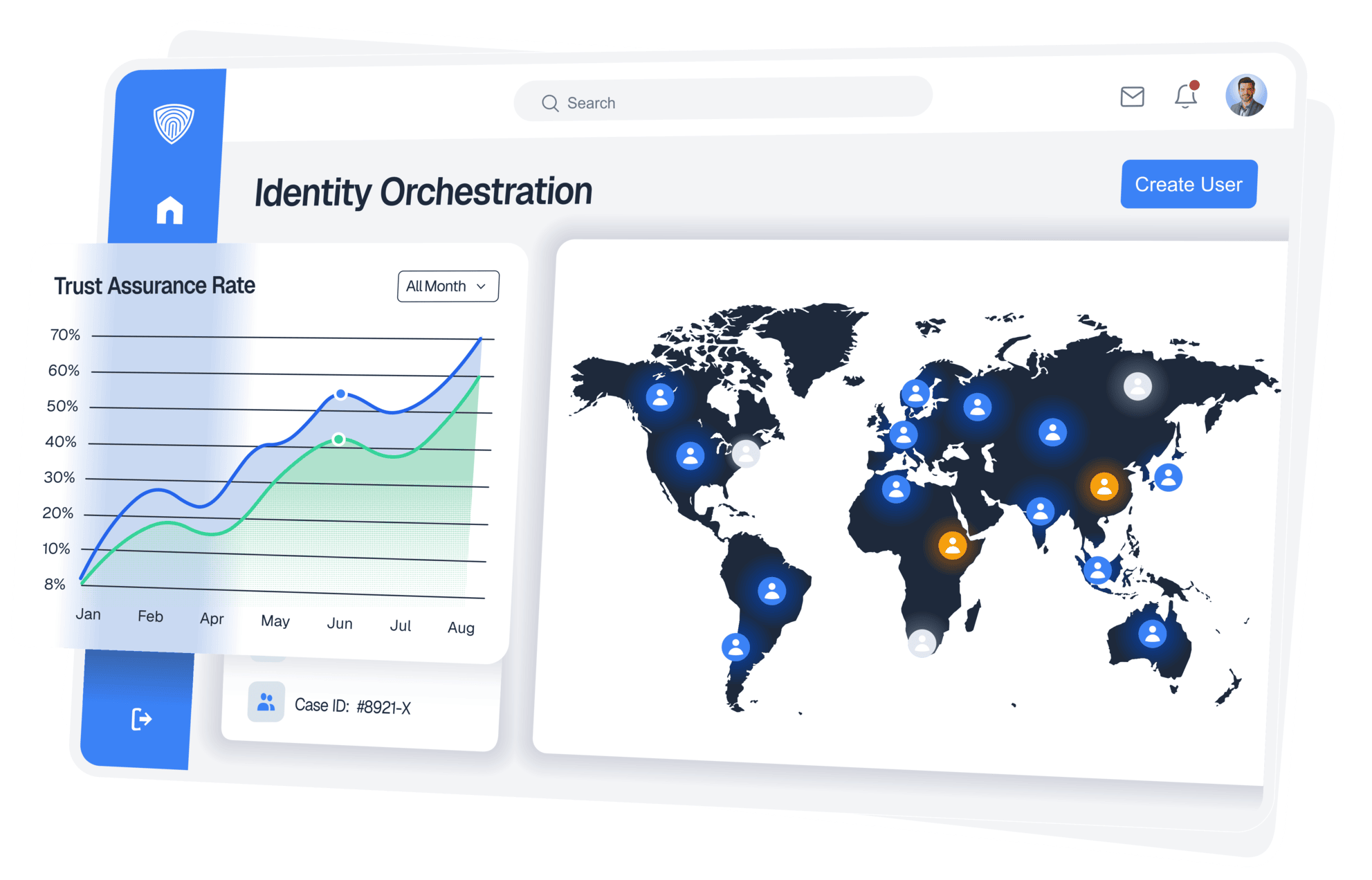
Enterprise Identity Platform
Run low-friction checks for standard users and step up to FedRAMP-aligned IAL3 proofing when risk is high.
Use one platform for onboarding, re-verification, and account recovery with audit-ready evidence.
Customer Evidence
Powering over 1 Million verifications for businesses in 20+ countries.
Apply the right assurance level at the right point in each workflow.
Trigger stronger verification only when signals indicate risk, so low-risk users move quickly while high-risk events get deeper checks.
Support KYC, AML, and regional policy requirements with configurable controls built for regulated teams.
Capture verification decisions, approvals, and artifacts in a format security and compliance teams can review and defend.
Use supervised workflows, liveness checks, and hardware-assisted NFC document verification for high-risk users.

When standard verification is not enough, deploy supervised remote proofing with controlled hardware and traceable evidence.

Connect identity decisioning to your IAM, HR, and internal tools through APIs and webhooks without rebuilding your workflows.
Outcomes
Replace fragmented tools with one defensible identity workflow.

Plan Your Identity Assurance Rollout